[ad_1]
In this posting, QA engineer on the launch group at inDriver Ivan would like to let himself to freely speculate on the similarity between cognitive exercise versions in software package screening and criminal investigations.
It appears to be to me that these two locations have a ton in common. For case in point, each procedures are focused on investigating the results of misconduct, as well as its leads to and effects, alongside with similar information-maintaining and documentation procedures.
A calendar year in the past, I got an offer you for the function of QA Manual Engineer at inDriver. But ahead of that, I used 7 yrs investigating prison situations at a variety of legislation enforcement units and agencies. In the course of my service, I worked with a extensive variety of legal offenses, from really serious crimes that endanger a person’s lifetime and well being to economic crimes of an interregional character. At my final career, my occupation title was: “Senior Investigator of the Investigative Division for Combating Arranged Criminal offense of the Investigative Directorate of the Ministry of Inner Affairs of the Republic of Sakha (Yakutia)”
Now my work is to set up regression testing, produce cell UI autotests, and get care of several other factors built to speed up the procedure of delivering new attributes to end users devoid of any reduction in item excellent.
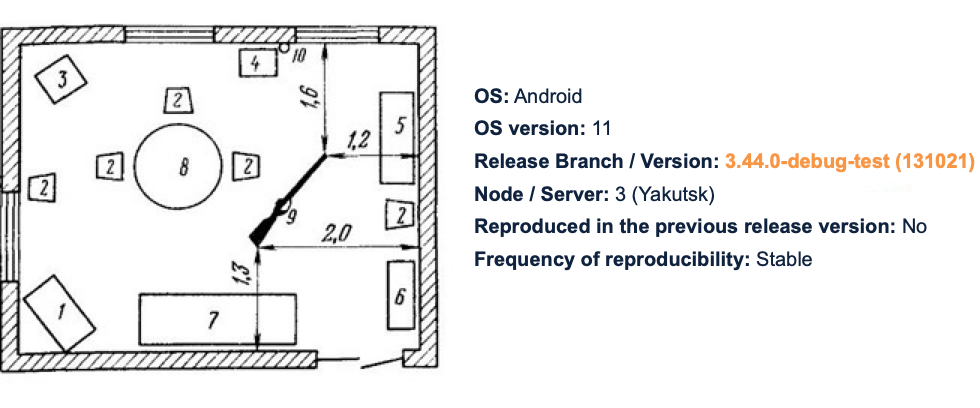
Just as a legal investigation starts with inspecting the crime scene, the bug report starts with a description of the surroundings the place the defect was located. In this way, we acquire some reliable and trusted data. Then, applying that facts as a basis, and making use of a deductive tactic, as effectively as our information about the atmosphere or the products, we can slender down the region of investigation, and start organizing further moves and establish our assumptions.
After we get the raw knowledge, we are faced with info diversity. Now it is significant to attract up an action approach. Time is our number-one useful resource here. It would hardly be a superior idea to check all values from -2,147,483,648 to 2,147,483,647 in the identify input area with a see to locating the defect. In the same way, the investigator does not have the capability to issue all of the town’s people or deliver just about every solitary residence utensil or merchandise for molecular genetic testing.

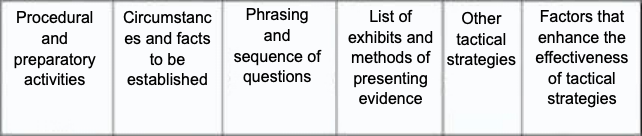
To take care of this challenge, the QA engineer applies take a look at design methods focusing on boundary values, equivalence courses, and pairwise. In contrast, investigators will utilize strategies and combos that make it doable for them to system their more ways as successfully as feasible.
Suppose we receive a murderreport to the influence that we experienced a crash in our application. From my experience as an investigator, I know that pretty much 90 p.c of all murders are linked in just one way or one more to the victim’s spouse, wife, kinfolk, mates, or neighbors. It’s the exact tale with the app…we are guided by product or service expertise: let’s say we pull out a sniffer, and check out the outgoing requests and the responses we get. So considerably, very little interesting: all the spouse and children associates have alibis, and the reaction from the server is made up of “200.” Every thing appears to be to be in get right here.

Also, we know that a person of audio intellect would not commit murder devoid of a motive. Primarily based on that, we can slim down an unlimited list of suspects to those with whom the target was linked fiscally or had do the job-associated or some other contacts. Likewise, in the application we can establish the release version from which the defect commences to propagate, and produce our assumptions about what variations in the code could have induced the bug to surface.
Following, we check out to set up all the activities that preceded the criminal offense in get to monitor down some incriminating proof:
- We view footage from movie cameras.
- We interrogate neighbors to uncover out if they read the seems of a wrestle or observed any suspicious individuals.
- We establish who the victim spoke with on the cellphone soon before the crime was fully commited.
When dealing with a defect, we also accumulate evidence:
- We capture logs in Android Studio or XCode.
- We check the server logs.
In the process, we come across out that a male NullPointerException entered the condominium soon ahead of the crime was fully commited. Neighbors determined him as a local compact-time hoodlum with a felony report who routinely obtained drunk and was feared by all the tenants of the setting up.

Let’s suppose that, as soon as the incriminating proof is generated, the man confesses to the criminal offense. The investigation doesn’t close there. We have to make guaranteed that it was him who fully commited the criminal offense, and that his confession of guilt is enthusiastic by remorse, fairly than the panic of spoiling the investigator’s mood.
For this goal, the proof is confirmed at the internet site of the criminal offense, where by the accused perpetrator is demanded to reveal the entire facts of the criminal offense and recount any circumstances that aren’t regarded to any party who is not associated in the commission of the crime. Therefore, by pinpointing a steady scenario for the replica of the defect, we obtained conclusive evidence that we had located the proper occasion we had been hunting for.
The moment all the circumstances of the criminal offense have been recognized, it is not the investigator’s work to rectify the defect. He organizes gathered proof into the prison scenario file, attracts up an indictment, and submits it to the court docket of legislation. The choice on sentencing, on how to deal with the bug, or on no matter whether to declare this bug an innocent aspect is made outdoors of the screening course of action.

In get to avoid identical offenses in the upcoming, the investigator ought to set up the situations that contributed to the fee of the criminal offense less than evaluation and get related action. He or she will have to build, for instance, the motive why no ways were being taken beforehand in response to reports about the perpetrator’s conduct, or why the actions taken from him unsuccessful to stop the criminal offense.
The similar is real in the situation of tests: when a bug is detected on PROD, it would not damage to detect the variables that contributed to its look:
- Inadequate take a look at protection.
- Merge with no exam protection.
- Weak problem formulation.
- Inadequately described specifications.
- Corner conditions not checked by a QA professional.
- An insufficient total of time allotted for testing and development uses.
- Small professional skills of growth crew members.
- Usually transforming prerequisites.
Of course, the work opportunities of an investigator and a tester are not the very same. Some frequent attributes notwithstanding, there are even now noticeably far more variations than similarities involving them. But if for any explanation you find on your own confronted with a want to radically change your occupation trajectory, you can find appropriate courses from our partner, and this is feasible. Even in a entirely distinctive field, you can find things to do that involve a equivalent attitude — and that will make it a minor less complicated to realize the purpose you have set oneself.
[ad_2]
Source backlink